Patch Management Software for Every OS in Your Environment
Automate server patch management across Windows, Linux, Solaris, and AIX from a single console. JetPatch replaces fragmented patching tools with one governed, end-to-end workflow — from discovery through deployment to compliance reporting.
End-to-End Patch Management in Five Steps
JetPatch governs the entire remediation lifecycle — from the moment a vulnerability is disclosed to the moment your auditor gets a signed compliance report. Every step is automated, auditable, and repeatable.
Automatically discover every server, VM, and endpoint across vCenter, AWS, Azure, Active Directory, and WSUS. Build a complete asset inventory with OS versions, installed patches, and configuration state. JetPatch imports tags from cloud providers and maps endpoints into Smart Groups for targeted patching policies.
Run real-time gap analysis using the Patches Catalog. Identify missing security updates, filter by severity and CVE, and build Patch Bundles (Saved Filters) that target exactly what needs remediation. The Patches Catalog shows the status of every patch across your entire environment in real time.
Before deploying, run Predictive Patching to simulate the cycle. Identify offline machines, credential issues, disk space problems, and dependency conflicts — then resolve them before the maintenance window.
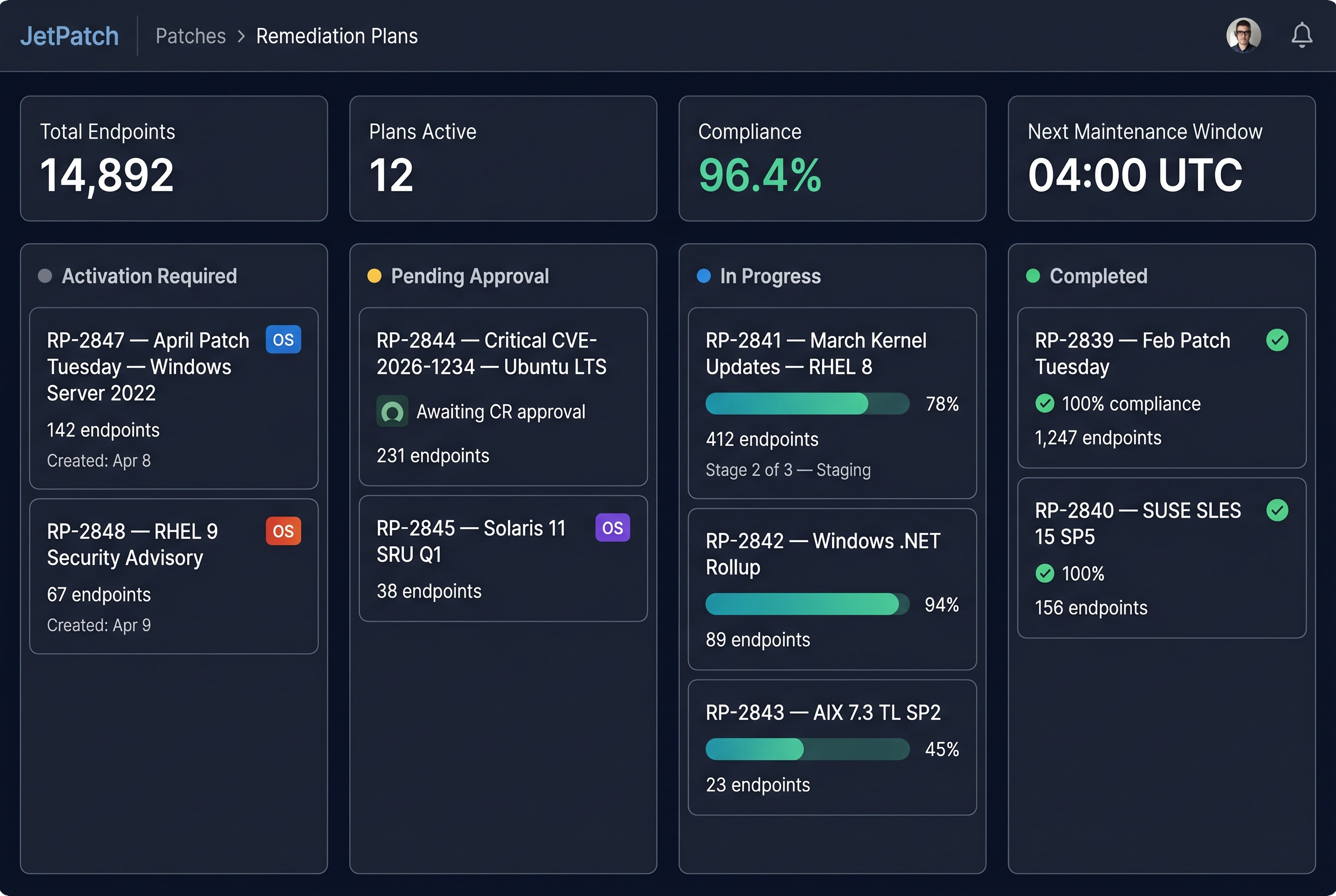
Execute Remediation Plans through sequenced rollouts — QA first, then staging, then production. Maintenance schedules ensure deployment happens within approved change windows with SLA tracking. If ITSM is configured, deployment waits for change request approval from ServiceNow or Jira before proceeding.
Generate compliance reports showing patch status by OS, environment, and remediation plan. Export CSV and PDF reports for NIST, CIS Controls, PCI-DSS, and HIPAA audits. Track SLA adherence in real time. Dashboards show Effective Compliance and Total Compliance breakdowns by OS family, environment, and remediation plan status.
One Platform. Every Operating System.
Unlike tools that only handle Windows or mainstream Linux, JetPatch provides native automated patching for every OS family in your environment — including the legacy Unix platforms that most vendors cannot support.
- ✓ WSUS bidirectional group sync or WSUS-less cloud mode
- ✓ Third-party app patching (Chrome, Java, Adobe, AnyDesk, and more) via proprietary JetPatch catalog
- ✓ Intune policy support for hybrid environments
- ✓ Feature updates, security rollups, and definition updates

- ✓ Advisory-level patching with CVE correlation
- ✓ Unified local repository management across distributions
- ✓ Kernel and non-kernel security patches
- ✓ Rollback support for JetPatch-installed patches
- ✓ Solaris CPUs via JetPatch local repository
- ✓ AIX patching through NIM repository integration
- ✓ Same predictive patching and compliance features as Windows/Linux
- ✓ Critical for energy, financial services, and government environments
Everything You Need to Patch at Enterprise Scale
JetPatch was built for environments where patching is complex, multi-team, and compliance-critical. These are the capabilities that make it possible.
Discover endpoints across vCenter, AWS EC2, Azure, Active Directory, and WSUS. Import tags from cloud providers. Automatically classify devices into Smart Groups for targeted patching.
A centralized catalog of all available patches with real-time visibility into what's installed, missing, approved, or declined. Create Saved Filters (Patch Bundles) for recurring remediation workflows.
Simulate the entire patch cycle before deployment. Identify offline machines, credential failures, low disk space, and dependency conflicts. Maximize first-pass success rates within your maintenance window.
Build manual or automatic remediation plans with SLA tracking, ITSM approval gates, and configurable pre- and post-patching workflow tasks. Plans support emergency zero-day response and scheduled maintenance.
Orchestrate multi-stage rollouts across QA, staging, and production. Define success criteria per stage (e.g., "80% of endpoints at 95% compliance") before advancing to the next environment.
Prevent specific patches from being deployed to certain machines while still meeting overall compliance targets. Block kernel patches on sensitive servers or .NET updates on legacy applications.
Validate that every endpoint is ready to receive patches before deployment begins. Check repository connectivity, disk space, OS support status, and WSUS communication health.
Roll back patches that cause issues after deployment. JetPatch supports rollback for Linux and Unix patches it installs, and declined patches can be revoked from approved states across all remediation plans.
Generate audit-ready reports in CSV and PDF. Track compliance by OS, environment, Smart Group, and remediation plan. Real-time dashboards show Effective Compliance and Total Compliance with SLA status.
Connects to Your ITSM, Vulnerability Scanners, and Cloud Infrastructure
JetPatch integrates bidirectionally with the tools your IT operations and security teams already use — ensuring automated change management, vulnerability-driven prioritization, and full audit trails.
ITSM, Vulnerability, and Cloud Integration
Remediation plans in JetPatch trigger change requests in your ITSM automatically. Deployment proceeds only after approval. Vulnerability scanner data feeds directly into patch prioritization, and cloud discovery sources keep your asset inventory current.
- ✓ ServiceNow bidirectional change management with CI matching and maintenance window sync
- ✓ Jira and Symphony Summit ticket automation for remediation plan approval
- ✓ Qualys, Tenable, and Rapid7 vulnerability feed integration for risk-based prioritization
- ✓ AWS EC2, Azure, vCenter, and Active Directory discovery sources
- ✓ REST API for ITSM automation and custom reporting workflows
What Makes JetPatch Different from Other Patching Tools
Most patching tools automate deployment for Windows and a few Linux distributions. JetPatch was built for a different problem: governed, end-to-end vulnerability remediation across the full complexity of enterprise IT — where patching spans 20+ operating systems, multiple data centers, strict change management processes, and regulatory compliance requirements that most tools were never designed to handle.
-
✓
Deepest OS coverage in the market Windows, 9+ Linux distributions, Oracle Solaris, and IBM AIX from one console. Competitors like NinjaOne, ManageEngine, and Ivanti do not natively support Solaris or AIX patching.
-
✓
Predictive Patching The only platform that simulates the entire patch cycle before deployment, exposing blockers in advance so teams achieve maximum success rates within every maintenance window.
-
✓
Sequence Patching with success criteria Multi-stage rollouts with configurable thresholds per environment — not just scheduling, but governed progression from QA through production.
-
✓
ITSM-governed change management Bidirectional ServiceNow and Jira integration that blocks deployment until change requests are approved, with maintenance window sync from CMDB.
-
✓
Forbes Global 2000 proven Deployed at National Grid, Philips, Ramsay Health Care, Airtel, Woodside, and other enterprises managing thousands of critical endpoints.
What IT Leaders Say About JetPatch Patch Management
JetPatch holds a 4.5-star average across G2, Gartner Peer Insights, and Capterra — rated by operations leaders managing thousands of servers daily.
“Using the JetPatch platform, we were able to quickly and efficiently extend modern patch management services to our large customer base. The smart automation transforms our Managed Services team’s capability to handle customer risk and compliance efficiently.”
“With JetPatch we have consolidated and automated our Patch Management process, which significantly reduced our IT Operations Cost and Time-To-Remediation of our IT infrastructure.”
“This product keeps all infrastructure and servers up to date as per business requirement. It helps me save a lot of time and eliminates manual, repetitive tasks.”
Patch Management — Technical Details
Answers for IT operations leaders, security architects, and compliance officers evaluating enterprise patching platforms.
What operating systems does JetPatch support?
JetPatch supports 20+ platforms: Windows Server (2016 through 2025), Red Hat Enterprise Linux 7-9, Ubuntu LTS, SUSE Linux Enterprise Server 12-15, Debian, CentOS, Rocky Linux, AlmaLinux, Amazon Linux, Oracle Solaris 10 and 11, IBM AIX 7.x, and macOS (Intel, with ARM support coming). All are managed from one console with unified compliance dashboards.
How does Windows patching work in JetPatch?
JetPatch integrates with WSUS using bidirectional Smart Group synchronization — it pulls endpoint data and patch status from WSUS, then controls approval and deployment through Remediation Plans. With version 4.2.8+, JetPatch also supports WSUS-less mode where Windows endpoints retrieve updates directly from Microsoft Update, ideal for cloud and remote workforce scenarios. Both modes support third-party application patching through a proprietary JetPatch catalog plugin.
How does Linux patching differ from Windows in JetPatch?
Linux patching in JetPatch uses native package managers (YUM/DNF for RHEL-family, APT for Debian/Ubuntu, Zypper for SUSE) with advisory-level patch identification. JetPatch manages local repositories to ensure consistent patch availability, and scan schedules run via configurable cron jobs. Rollback is supported for patches installed by JetPatch. Unlike Windows, no external infrastructure like WSUS is required.
Can JetPatch patch Oracle Solaris and IBM AIX?
Yes — this is one of JetPatch's strongest differentiators. Solaris 10 uses a proprietary JetPatch local repository for caching Critical Patch Updates (CPUs), while Solaris 11 uses IPS repositories. AIX patching uses NIM repository integration. Both receive the same predictive patching, sequence deployment, and compliance reporting available for Windows and Linux. The JetPatch connector for Solaris requires approximately 700MB of disk space.
What is Predictive Patching and how does it work?
Predictive Patching, introduced in JetPatch v4.0, runs a fast simulation of the planned patch cycle before actual deployment. It correlates data from multiple sources to expose potential blockers: machines that are powered off, invalid or expired credentials, insufficient disk space, unknown dependencies, and misconfigured repositories. The output is an expected success rate and a detailed list of issues to resolve, allowing teams to achieve near-100% first-pass success within their maintenance window.
How does Sequence Patching work?
Sequence Patching lets you chain multiple Remediation Plans into an ordered, multi-stage rollout. Each stage has configurable success criteria — for example, "80% of endpoints must reach 95% compliance before advancing." Stages can require manual approval or auto-advance when criteria are met. This is typically used for QA → staging → pre-production → production rollouts in regulated environments.
Ready to Simplify Patch Management Across 20+ Operating Systems?
Whether you manage 500 or 25,000 servers, 1,000 or 50,000 endpoints, JetPatch scales to your environment. Start with a free trial, schedule a walkthrough, or calculate the ROI for your team.
Schedule a Demo
See JetPatch in action with a guided walkthrough tailored to your environment.
Schedule a DemoCalculate Your ROI
See how much time and money JetPatch can save your team. Takes 60 seconds.
Open ROI Calculator →